I quickly scanned and no mention will gov fund to projects they uses. Nice.
Aegis w/ auto backup + syncthing
Spammer. He already made 14 posts with the same thing. Along with @testinghead@lemmy.ml and @testinghead@lemmy.world. I bet it is the same guy.
Spammer. He already made 14 posts with the same thing. Along with @testinghead@lemmy.ml and @testinghead@lemmy.world. I bet it is the same guy.
How about no lock in from the get go?
Missing file I can understand, but how they infect the user with malware? Is it through the BitTorrent protocol, or undisclosed vulnerbility of the Grid Service? The kill chain isn't complete.
P.S. The use of BitTorrent in Korea by service providers is somehow justified IMO given how expensive the bandwidth is which Twitch quit the market.
How many know what even signed commit and build is? For people following a guide they don't even know what Github is for but a nice place to have free programs.
Just tell them unlock their phone so you can take a look of his browser history. Works quite a few time for me.
When they mirror it, does they uses a different username? If so I'm totally fine as that's just a fork, otherwise it should count as stolen. Not the project but the name and reputation of the owner.
I have simplex notification service running 24x7. while rarely open, i never missed a message when it arrive (i use it as a message bridge between my devices). Nor I feel it uses more battery that it can't hold a day of use despite it running constantly in the background. I'm using S21FE btw.
OpenBao, fork from vault
Define your criteria for an ideal messenger. What do you need actually? What's your security requirement?
Well. The claim they made still holds true, despit how I dislike this design choice. It is faster, and more secure (though attacks on NAND chips are hard and require high skill levels that most attacker won't posses).
And add one more: it saves power when using LPDDR5 rather DDR5. To a laptop that battery life matters a lot, I agree that's important. However, I have no idea how much standby or active time it gain by using LPDDR5.
Parts pairing will do. That's what Apple known for, knee capping consumer rights.
I usually take BDRAW, transcode by myself. Or the best quality I can find. Does it look better? Not really. Just the data hoarder inside kicked in. 720p is totally fine.
forfeit the revenue that they earn during the period for this
I like this. This will give them the urgency and motivation to plug the hole ASAP, rather stall and repeat the cycle.
IMO 12 mo is too much. They will wait till the dead line to public the "fix."
Addition. Use a Makefile to push and deploy in one make command.
GH action is all what you need. If you really worried open ssh over the internet, use Tailscale or Cloudflare Tunnel. Or use a firewall rule to block off traffic except from GH IP ranges. TBH, I have VPSes that have SSH open to the whole world. Yes, it got many hits everyday but they doesn't do anything beyond that.
Chinese shopping platform Pandabuy told BleepingComputer it previously paid a a ransom demand to prevent stolen data from being leaked, only for the same threat actor to extort the company again this week.

LOL
Republican state Rep. Alex Kolodin says he used the artificial intelligence software to help define a subsection of a bill Gov. Katie Hobbs signed into law.

Shall we trust LM defining legal definitions, deepfake in this case? It seems the state rep. is unable to proof read the model output as he is "really struggling with the technical aspects of how to define what a deepfake was."
Recently I just hit by stolen card detail and makes me searching a virtual card service. Anyone knows any works in the UK and EU region? Apparently Privacy.com needs SSN to work now. Thanks.
The FBI, UK National Crime Agency, and Europol have unveiled sweeping indictments and sanctions against the admin of the LockBit ransomware operation, with the identity of the Russian threat actor revealed for the first time.

Require publishers to leave videogames (and related game assets / features) they have sold to customers in a reasonably working state when support ends, so that no further intervention whatsoever is necessary for the game to function, as a statutory consumer right.

tl;dr: we will do nothing about it
Full response below
---
The Government recognises recent concerns raised by video games users regarding the long-term operability of purchased products.
Consumers should be aware that there is no requirement in UK law compelling software companies and providers to support older versions of their operating systems, software or connected products. There may be occasions where companies make commercial decisions based on the high running costs of maintaining older servers for video games that have declining user bases. However, video games sellers must comply with existing consumer law, including the Consumer Rights Act 2015 (CRA) and the Consumer Protection from Unfair Trading Regulations 2008 (CPRs).
The CPRs require information to consumers to be clear and correct, and prohibit commercial practices which through false information or misleading omissions cause the average consumer to make a different choice, for example, to purchase goods or services they would not otherwise have purchased. The regulations prohibit commercial practices which omit or hide information which the average consumer needs to make an informed choice, and prohibits traders from providing material information in an unclear, unintelligible, ambiguous or untimely manner. If consumers are led to believe that a game will remain playable indefinitely for certain systems, despite the end of physical support, the CPRs may require that the game remains technically feasible (for example, available offline) to play under those circumstances.
The CPRs are enforced by Trading Standards and the Competition and Markets Authority. If consumers believe that there has been a breach of these regulations, they should report the matter in the first instance to the Citizens Advice consumer helpline on 0808 223 1133 (www.citizensadvice.org.uk). People living in Scotland should contact Advice Direct Scotland on 0808 164 6000 (www.consumeradvice.scot). Both helplines offer a free service advising consumers on their rights and how best to take their case forward. The helplines will refer complaints to Trading Standards services where appropriate. Consumers can also pursue private redress through the courts where a trader has provided misleading information on a product.
The CRA gives consumers important rights when they make a contract with a trader for the supply of digital content. This includes requiring digital content to be of satisfactory quality, fit for a particular purpose and as described by the seller. It can be difficult and expensive for businesses to maintain dedicated support for old software, particularly if it needs to interact with modern hardware, apps and websites, but if software is being offered for sale that is not supported by the provider, then this should be made clear.
If the digital content does not meet these quality rights, the consumer has the right to a repair or replacement of the digital content. If a repair or replacement is not possible, or does not fix the problem, then the consumer will be entitled to some money back or a price reduction which can be up to 100% of the cost of the digital content. These rights apply to intangible digital content like computer software or a PC game, as well as digital content in a tangible form like a physical copy of a video game. The CRA has a time limit of up to six years after a breach of contract during which a consumer can take legal action.
The standards outlined above apply to digital content where there is a contractual right of the trader or a third party to modify or update the digital content. In practice, this means that a trader or third party can upgrade, fix, enhance and improve the features of digital content so long as it continues to match any description given by the trader and continues to conform with any pre-contract information including main characteristics, functionality and compatibility provided by the trader, unless varied by express agreement.
Consumers should also be aware that while there is a statutory right for goods (including intangible digital content) to be of a satisfactory quality, that will only be breached if they are not of the standard which a reasonable person would consider to be satisfactory, taking into account circumstances including the price and any description given. For example, a manufacturer’s support for a mobile phone is likely to be withdrawn as they launch new models. It will remain usable but without, for example, security updates, and over time some app developers may decide to withdraw support.
Department Culture, Media & Sport
Royal Mail, the British postal and courier service began switching all snail mail stamps to barcoded stamps last year. The purpose of the barcode was to enhance security, deter stamp reuse, and possibly prevent forgeries—which it has failed to do.

If a stamp have a barcode, why not just let people who have printers at home to print it on the envelope directly? This eliminates the need to buy physical stamp, thus the probability of buying counterfeit stamps.
I want to host a small game server for friends and myself in my home but doesn't want to open up the firewall. Any tunneling solutions supports UDP? Thnaks.
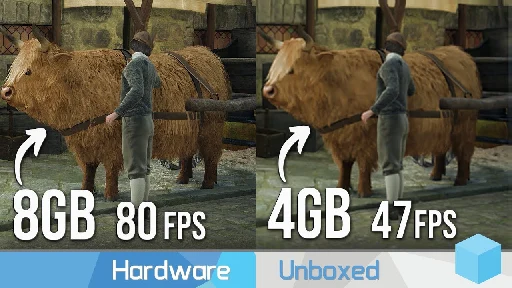
Anyone tried it? I'm planning but saw the benchmark is pretty bad. Unsure if I interpret correctly.

YouTube Video
Click to view this content.
As a PC player, I never grasp why console players are willing to pay a ransom to access a product and service they already paid for.
And worst, this video shows M$ double dip dev by taking a 30% cut plus the cost of game service (like logins, verification, lobby, etc) unlike Steam that already have it covered in that cut, and triple dip by asking player to pay more.
As IBM highlights, existing FlashSystem products already scan all incoming data as it is being written, without impacting performance. The new AI-enhanced FlashCore Module 4 (FCM) is...

Am I too pessimistic about this? Today it can detect ransomware, the next day could be malware, and the day after can be any file.
It's just a data filter that's build in to a hardware and possibly no way to trun off. Last thing I want is a black box watching what I stored on my drive.
cross-posted from: https://lemmy.ml/post/12593641
> I want to share some images securely with self destruct. Is there any alternatives can do what Unsee.cc does excluding chat? > > So the functions I'm looking for: > - Self-expiring image > - Copy protection > - Store in RAM > - (optional) watermarking > - (optional) share more types of documents like PDF > > Thanks in advance.
I want to share some images securely with self destruct. Is there any alternatives can do what Unsee.cc does excluding chat?
So the functions I'm looking for:
- Self-expiring image
- Copy protection
- Store in RAM
- (optional) watermarking
- (optional) share more types of documents like PDF
Thanks in advance.
I'm setting up FDE and wonders which one is better. "LVM over LUKS" or "LUKS over LVM"? Or something else? Does one is definitely better then the other? What are your preference?
Thanks.
Google during a testimony in the Epic vs Google trial said that a deal with Spotify allows the audio company to completely bypass Play Store fees.

NetBird combines a configuration-free peer-to-peer private network and a centralized access control system in a single cloud platform.
cross-posted from: https://lemmy.ml/post/8144135
> Just stumble it on YT. Anyone tried Netbird? How this compares to Tailscale w/ headscale?
NetBird combines a configuration-free peer-to-peer private network and a centralized access control system in a single cloud platform.
Just stumble it on YT. Anyone tried Netbird? How this compares to Tailscale w/ headscale?

TBH I have a mixed feeling about this.
The UK government has proposed using hash scanning to detect abusive material without violating people’s privacy. Unfortunately, it won’t work.

This is an continuation of my last post, specifically a comment from @rufus@discuss.tchncs.de:
> It will never get recommended. It’s bad for the network and bad for your privacy.
Excluding that doing so is bad for the network, why it is "private" using VPN but not Tor, inferring from common consensus. The main point in the blog post is a protocol level problem:
> apparently in some cases uTorrent, BitSpirit, and libTorrent simply write your IP address directly into the information they send to the tracker and/or to other peers
Tor and VPN are both transports what wrap other traffic within. If that statement is true, no transport can save the information leaking nature of the BT protocol itself.