gaining access to anyones browser without them even visiting a website
What a good browser...
a post going over 4 exploits for CVE-2024-20017, a remotely exploitable buffer overflow in a component of the MediaTek MT7622 SDK.
This is sso support as the client. So you could use any backend that supports the oauth backend (I assume, didn't look at it yet).
So you could use a forgejo instance, immediately making your git hosting instance a social platform, if you wanted.
Or use something as self hostable like hydra.
Or you can use the social platforms that already exist such as Google or Microsoft. Allowing faster onboarding to joining the fediverse. While allowing the issues that come with user creation to be passed onto a bigger player who already does verification. All of these features are up for your instance to decide on.
The best part, if you don't agree with what your instance decides on, you can migrate to one that has a policy that coincides with your values.
Hope that gives you an idea behind why this feature is warranted.
Possibly, as it's one generic endpoint, but it also blocked a few other things people in the fediverse created, which are mighty helpful in diagnosis of these and other issues.
So using some AI model or whatever CF uses is probably not going to be the best thing for us as it classified a POST request as a crawler?? 🤷
I'd have to whitelist every regular endpoint as well and then it gets messy as CF only gives you so much control as a free user.
So, for the moment I've blocked the most annoying ones based on UserAgent.
We enabled the CloudFlare AI bots and Crawlers mode around 0:00 UTC (20/Sept).
This was because we had a huge number of AI scrapers that were attempting to scan the whole lemmyverse.
It successfully blocked them... While also blocking federation 😴
I've disabled the block. Within the next hour we should see federation traffic come through.
Sorry for the unfortunate delay in new posts!
Tiff
Automated Encryption Framework. Contribute to latchset/clevis development by creating an account on GitHub.

to be paired with tang
Social media giants would be forced to ban children under the age of 14 from their platforms or face hefty penalties, under proposed laws in South Australia that could be replicated in other states.
Highly relevant to us (as admins)
A broadcast, in a box. . Contribute to Glimesh/broadcast-box development by creating an account on GitHub.

Not so much a sploit but an easy way to do broadcasting!
I can neither confirm or deny for the safety of my pigeons.
I recently had solar panels and a battery storage system from GivEnergy installed at my house. A major selling point for me was that they have a local network API which can be used to monitor and…

Tony Hawk's Pro Strcpy: A game save and RCE exploit for the Tony Hawk game series that can be used to hack Xbox, Playstation 2, Gamecube, and Xbox 360 consoles.

the "official" incident root cause analysis
Keys were labeled "DO NOT TRUST." Nearly 500 device models use them anyway.

An article from July, but I bet you haven't updated your bios! Or you left it open on purpose?
A really good article on how TPMs work
Yeah that's why I included the other "main posts"... Their technical details really didn't say anything technical
Learn more about the July 19, 2024 CrowdStrike outage and the technical details related to it.

The update that broke half of all enterprise servers. One of the official remediation steps is to "Reboot as many as 15 times"
Read more: https://community.intel.com/t5/Intel-vPro-Platform/Remediate-CrowdStrike-Falcon-update-issue-on-Windows-systems/m-p/1616593/thread-id/11795
- https://old.reddit.com/r/crowdstrike/comments/1e6vmkf/bsod_error_in_latest_crowdstrike_update/
- https://repost.aws/en/knowledge-center/ec2-instance-crowdstrike-agent
- https://azure.status.microsoft/en-gb/status
Update your openssh, now
This should be fixed as we rolled out 0.19.5 today
Oh I was wrong, after further reading this looks to be a lot better than what I was thinking.
I must have been thinking about another methodology of attempted privacy over a dataset.
Before I start reading, if this has anything to do with differential privacy, I'm going to be disappointed.
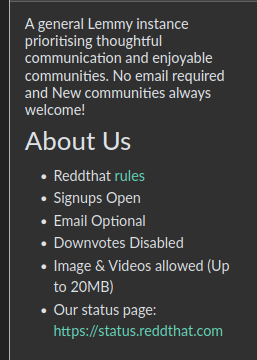
Yes, you can upload images to Reddthat when posting, commenting, etc.
We have a CDN In front and aggressively cache all of the images.
3rd party images are fetched to generate a thumbnail, and to cache the image. The problem with this is, catbox can be slow at times and if that happens when you post it can't generate them.
Some clients also only open the direct links instead of showing the cached image, resulting in images not loading, or taking forever to load.
I say if you are posting on Reddthat, I'm happy for people to use the features provided by Reddthat. So upload here, if you so wish.
Just remember that the images you upload are linked to your account.
2nd best reporting in.
A faster db. Just the regular performance benefits, https://www.postgresql.org/about/news/postgresql-16-released-2715/
Also, Lemmy is built against v16 (now) so at some point it will eventually no longer JustWork
The script will be useless to you, besides for referencing what to do.
Export, remove pg15, install pg16, import. I think you can streamline with both installed at once as they correctly version. You could also use the in place upgrade. Aptly named: pg_upgradeclusters
But updating to 0.19.4, you do not need to go to pg16... but... you should, because of the benefits!
This should be fixed now. After a re-deploy of 0.19.4 (as they repushed it ~6h after the initial tag)
We re-deployed 0.19.4 which had fixes. The emoji popup now shows up (for me on mobile)
Two years ago, something very strange happened to me while working from my home network. I was exploiting a blind XXE vulnerability that required an external HTTP server to smuggle out files, so I spun up an AWS box and ran a simple Python webserver to receive the traffic from the vulnerable server.

Unbelievable...
Drew always has a hot take about a problem
 Tiff @reddthat.com
Tiff @reddthat.com Self Proclaimed Internet user and Administrator of Reddthat